Need a few free hacking apps?
The more open Android platform offers a wide range.
I’ll show you the top 20 apps.
Let’s get started!
- 1 What are hacking apps?
- 2 The TOP 20 for Android
- 2.1 #1 Scan the network – cSploit
- 2.2 #2 Get control over IP packets – DroidSheep
- 2.3 #3 Unlimited exploits and possibilities – Kali NetHunter
- 2.4 #4 Stay hidden and undetected – Orbot
- 2.5 #5 Gain control over servers – Droid SSH
- 2.6 #6 All in one app – AndroidRat
- 2.7 #7 The digital search for evidence – MOBILedit Forensic
- 2.8 #8 Be able to install any app – ApkMirror
- 2.9 #9 A look inside every app – APKInspector
- 2.10 #10 Recover passwords – USB Cleaver
- 2.11 #11 Control your super-user power – Magisk
- 2.12 #12 The hidden keylogger – LokiBoard
- 2.13 #13 Scan and find WLAN – Fing Network Tools
- 2.14 #14 Virtual Box – pentesting on the computer
- 2.15 #15 Developer Power – Android Studio
- 2.16 #16 Antivirus Scanner – What’s inside?
- 2.17 #17 Hacking toolbox – Hackode
- 2.18 #18 Ingenious installer – TWRP
- 2.19 #19 Look inside – APK Extractor
- 2.20 #20 Game Guardian – Know every cheat
What are hacking apps?
These apps are Android applications that help white hats detect vulnerabilities in software anddiscover privacy liars.
The white hat examines apps, Wi-Fi networks and other devices to advise the owner on how a system administrator can optimise the security of the application or network.
These apps help you to re-engineer, better understand, manipulate or attack apps.
Are these applications dangerous?
Open source applications are not dangerous because you can view the source code publicly (Github). A criminal would hardly have a chance to integrate infected code into the app.
On the other hand, you have to blindly trust the provider of closed-source apps that the app itself is not malware. Check the reputation of the company before you make a purchase because the number of scams is constantly growing.
Isn’t that illegal?
Many journalists often portray hacking in a negative light.
The term “hacking” means that you solve a problem in an unusual, creative way. You can penetrate not only computers, but also furniture, homes, human bodies, time, vehicles, etc.
Steffen Lippke
An example: You have set yourself a goal, e.g. more beautiful furniture for your home.
The standard “textbook way” is the usual way of achieving your goal (buying new furniture). The own creative way (“hacking”) is e.g. spicing up and repurposing the furniture with new paint, shelves, decorative ribbons.
I have summarised when and why hacking is legal in this post.

What does it cost?
Many of these apps are available for free.
You can download them for free (e.g. open source apps). Some well-known manufacturers offer apps that are chargeable. Whether you trust them or not is up to you to decide. If you can read the source code and compile it yourself, then you can make sure of the security yourself.
Who uses them in the real business world?
These apps use penetration testers and white hats (IT security) to find security vulnerabilities in software and hardware. These apps are designed to get ahead of criminals and secure the applications.
An Android device is particularly well suited to checking wireless networks because the integrated W-LAN module can scan the networks.
How do they work?
Android is based on the Linux kernel and is a free operating system. You can view the source code and make changes yourself. This freedom allows programmers to write apps that can intervene deeply in the system.
Many tools work with Python scripts, for example, which attempt to exploit a vulnerability or misconfiguration. The aim of the hacking apps is to gain access to a target computer (and obtain administrator rights (root)).
The TOP 20 for Android
The following apps help white hats to find vulnerabilities and improve security:
#1 Scan the network – cSploit
This app is used by network penetration testers to test the security of a (wireless) network. Insecure configurations or incorrect settings mean that the internal network is insecure. It should be as difficult as possible for a third party to dial into the network.
#2 Get control over IP packets – DroidSheep
Penetration testers use this app to find out whether an app’s internet traffic is vulnerable and has security gaps.
The software can “stop”, modify and forward Internet packets so that you have full control over the network traffic.
The app only works on modified devices (rooting, LineageOS).
#3 Unlimited exploits and possibilities – Kali NetHunter
The most powerful app / system running on Android is the Kali Nethunter Suite.
Check out this tutorial if you want to learn about the Kali Linux desktop operating system in detail. This app brings some / all of the functionality to your mobile phone.
You can install this suite without root (NetHunter Rootless) or with root (NetHunter (Lite)). For example, you can execute Metasploit exploits via this app and run them against the target computer.
The Orbot app is a VPN that routes all internet traffic through the TOR network. The TOR network makes it impossible for third parties to trace you and you are anonymous.
#5 Gain control over servers – Droid SSH
White hats don’t need a touchscreen, they need a shell.
The SSH client D roid Shell is just right for geeks. You can connect to other servers and send commands to the server via a secure channel.
#6 All in one app – AndroidRat
This app enablesremote monitoring of the Android device completely.
For example, you can read call histories, SMS, GPS / location data.
In addition to reading, you can also control the device remotely: take photos remotely, record or play sound, make calls or send text messages. This app is handy if you are not within reach of your smartphone, for example.
#7 The digital search for evidence – MOBILedit Forensic
This app works together with the Windows software MOBILedit, which is designed for forensic smartphone investigations.
A forensic scientist uses the calls, images, apps and other data on the smartphone to reconstruct the course of events. The aim is to secure evidence and prevent criminals from covering their tracks.
#8 Be able to install any app – ApkMirror
This app store helps you to access apps that are not normally unblocked in your region. This process is similar to VPN apps that make video content available from other countries. (Geoblocking)
#9 A look inside every app – APKInspector
The APKInspector app helps you to extract the source code from an APK.
A whitebox pentest is more useful in most cases because the pentester gains deeper insights into the app. Many Android apps are based on Java. Every Java app can be easily decompiled as long as an obfuscation has obfuscated the code.
#10 Recover passwords – USB Cleaver
The USB Cleaver app enables passwords to be extracted from a switched-on Windows computer.
The tool can extractW-LAN, Firefox, Chrome and Internet Explorer passwords so that a locked-out user can log in again.
#11 Control your super-user power – Magisk
The Magisk app is a superuser manager that allows you to customise the root permissions on your smartphone.
To use the app, you need a rooted mobile phone and full access to your data (LineageOS).
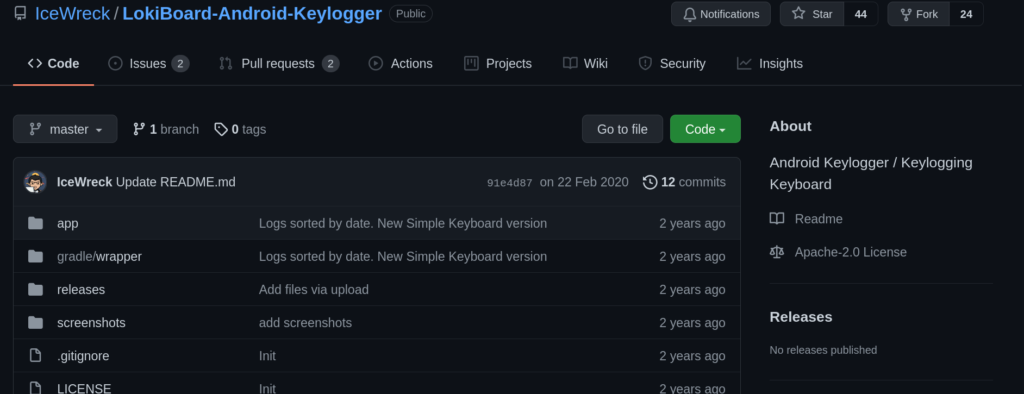
LokiBoard is a keylogger that looks like the normal Android / Google keyboard. From the user’s point of view, it works like a normal keyboard and saves the keystrokes in a file in the background.
#13 Scan and find WLAN – Fing Network Tools
This scanner helps you to analyse the network and find participants and identify network risks. A port scan and DNS lookup (domain to IP) is integrated into the app.
#14 Virtual Box – pentesting on the computer
If you want to check the security of a new app, a touch interface is unsuitable. Use your real computer and check how secure the application is with the familiar tools. With VirtualBox, you can simulate Android-x86 and control all environment parameters.
#15 Developer Power – Android Studio
In Android Studio you have full control over the app, instead of testing it compiled, you can monitor, control, switch off and manipulate everything from memory, logging and network.
#16 Antivirus Scanner – What’s inside?
Before you open an apk file, you should be sure whether it contains malware. A malware scanner will give you an initial indication. Despite the large malware databases, unknown malware is not included there.
#17 Hacking toolbox – Hackode
The Hackode app is a Schweitzer pocket knife of hacking. A multitude of practical little tools make the software a must-have.
#18 Ingenious installer – TWRP
If you want to install a custom Rom, then you need an Android recovery software. You flash the TWRP software onto your mobile phone and can install various operating systems, roots and application packages from there
#19 Look inside – APK Extractor
If you want to view the content of an APK, you have to extract it. Similar to a zip file, you extract images, code, logos, texts, etc. from the APK to examine them
#20 Game Guardian – Know every cheat
This cheat software is a must for every gamer. Play the games the way you want to play them and modify the apps so that you can beat your high score. Of course, you should not use these apps in competitions or a multiplayer game with a cheat ban.