Do you know the best 29 hacking tools for every ethical hacker?
What tools are available on the internet to crack passwords, search for vulnerabilities and to break out operating systems?
Here are the TOP 29!
- 1 Aren’t hacking tools illegal?
- 2 Password crackers
- 2.1 Cracking passwords with Bruteforce – Distributed Password Recovery
- 2.2 Cracking Windows – Offline NT Password & Registry Editor
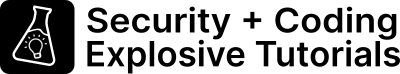
- 2.3 Make data visible in password hash – hashcat
- 2.4 Is my password leaked? – Pwnd
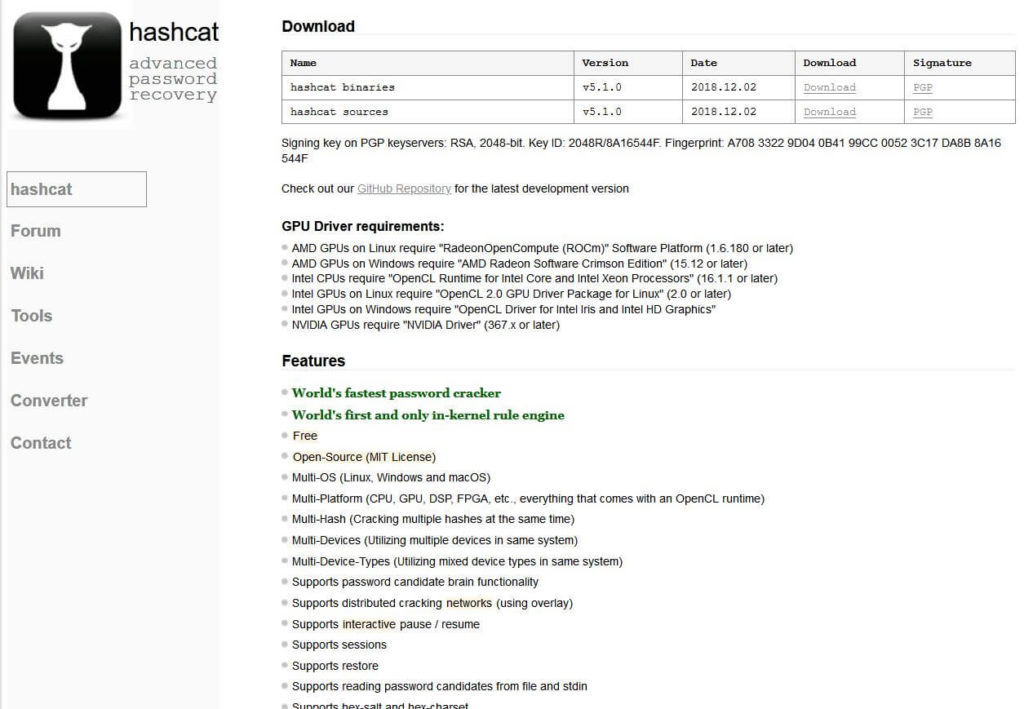
- 2.5 Windows password cracker for everything – Chain & Abel
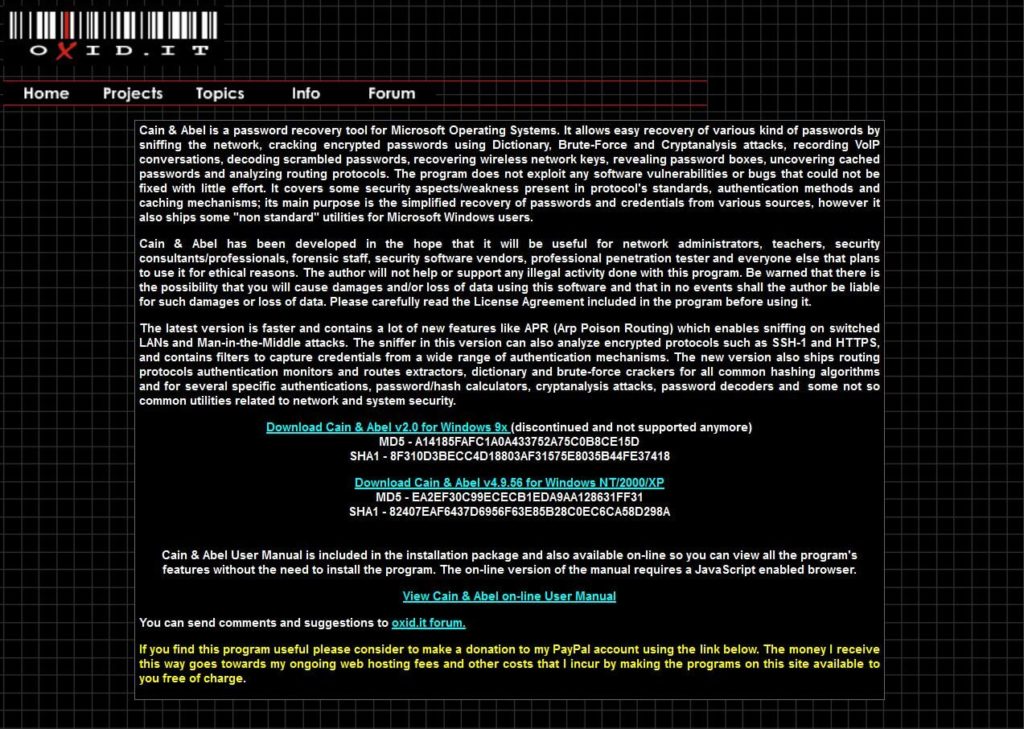
- 2.6 Reverse password guessing with rainbow tables – RainbowCrack
- 3 Vulnerability search for websites
- 4 Operating system vulnerability search
- 5 Wifi cracker
- 6 Network scanner
- 6.1 Who is on the network? Network Scanner Nmap
- 6.2 Password spying and snitches – network monitor Wireshark
- 6.3 Analyse WordPress – Wpscan
- 6.4 Where are the gateways? The ports – Postscanner
- 6.5 Scan the whole internet – Masscan
- 6.6 Vulnerability scanner for the whole network – Nessus
- 6.7 Mobile network and vulnerability scanner – dSpoilt
- 6.8 Enterprise risk scanner – zBang Tool
- 6.9 What’s on the network? Network Scanner – Angry IP Scanner
- 7 Other tools
Aren’t hacking tools illegal?
This list should be illegal!
Breaking into other people’s systems without permission is not allowed – hacking your own system is allowed. Companies lock themselves out of their own systems:
- The admin falls off his bike
- A system update goes wrong
- The boss suddenly dies (incl. passwords)
Tools are made for these purposes. Criminals often use the same tools – but they pursue a different goal.
A cook uses a knife to prepare food. A criminal uses a knife to stab his victims. The knife is a tool of the computer scientist.
Steffen Lippke
More on the question: Is hacking legal? Software like Mimikatz only have a harmful function (reading passwords) and are unnecessary for a pentest. The observation that I have penetrated a system is enough.
Transfer to a fight with armour and sword: As an honourable attacker, you would not still stab into the open part of the armour when the opponent is already unconscious. Nevertheless, you need to know this software in order to develop countermeasures.
Password crackers
Password crackers use white hats to gain access to systems from which the system admin has forgotten the password or has locked himself out.
Cracking passwords with Bruteforce – Distributed Password Recovery

ElcomSoft cracks up to 300 file types using CPU and GPU acceleration to brute-force the password. The software uses several computers in parallel to crack the password. The software can be executed remotely.
Cracking Windows – Offline NT Password & Registry Editor
Offline NT overwrites the Windows password on the hard disk so that you can change it. The Windows password can be reset from a USB stick.
Make data visible in password hash – hashcat
If you want to crack passwords professionally, use hashcat. Using parallelism (multithreading) on CPUs, the software is better than most rule-based brute force tools.
Is my password leaked? – Pwnd
Use Have I Been Pwnd to find out if your password has already been leaked in a databreach. If you don’t trust the online version you can download Databreach (large).
Windows password cracker for everything – Chain & Abel
Since Windows NT until Windows 8 Chain & Abel was the solution for forgotten Windows passwords. The tool is suitable for sniffing network traffic and for brute force attacks.
Reverse password guessing with rainbow tables – RainbowCrack
With the Rainbow tables, the white hats try to guess the password based on the given cryptographic hash. This way is in some cases faster than a normal brute force attack.
Vulnerability search for websites
… the Angular, React or Vue app is finally programmed and installed! Do you know the security problems of the new app? Pentesters search for the vulnerabilities in websites with these tools.
Database destroyer and manipulator – sqlmap
Do you know how SQL injections works? The right SQL commands leverage passwords, delete databases and change entries. The tool SQLmap automates the search for intrusion points for you.
Vulnerabilities in websites – finding exploits – Fortify WebInspect
Fortify finds and solves security problems in web applications. Angular, Ionic, Vue, React and Co applications are not always programmed correctly, so criminals don’t have a chance.
Websites – Burp Suite

The all-in-one tool, the Schweitzer pocket knife for website pentesters, is the Burp Suite. Try to crash the backend with cunning brup tricks, extract information or manipulate data.
Logger ++ – Upgrade for Burp Suite
This tool allows you to upgrade Burp Suite with a logging filter that brings powerful filtering capabilities to work with Burp.
Operating system vulnerability search
Have you ever forgotten a password for your operating system? No problem. These tools give you access to accounts with forgotten passwords. White hats use these tools to help clueless computer users “gain access”.
Gain power over Windows – Pentester tool Cobalt Strike

Take power over other people’s computers with remote access via the latest exploits! Cobalt Strike is a professional tool for pentesters who can hack into and control computers, e.g. with Spear Phishing.
Find and test all vulnerabilities – Vulnerabilities with Metasploit
Metasploit is used to exploit and validate vulnerabilities. The programme helps penetration testers with secure coding.
The procedure looks like this:
- Create a project
- Get data about your target
- Search for vulnerabilities
- Place a digital bug
- Exploit known vulnerabilities
- Exploit vulnerabilities undo
- Create a report
Wifi cracker
Use any wifi for free – Aircrack ng
As written in my wifi cracking tutorial, Aircrack-NG is suitable for breaking wifi encryption. An external antenna is often necessary for the computer.
Where are open wlans? – Kismet
The software Kismet searches for Wlan devices, serves as an Internet sniffer and detects Bluetooth signals. Using such software, criminals target cities in order to abuse open wlans for their own purposes or to alert the owner to the risk.
Man-in-the-Middle Practice Tool – Ettercap
Man-in-the-Middle in Real Life? You want more than the theoretical stuff? Use Ettercap! If a person intercepts the signal during transmission (hotspot laptop “Starbucks Coffee Public Wifi”), the network admin can read your internet traffic if certain conditions are met.
Network scanner
Do we have an intruder in our network?
With these tools white hats know what’s going on in the network!
Is there a server spying on our network?
Who is on the network? Network Scanner Nmap
With Nmap you can scan large networks in a few minutes or scan all ports of single hosts.
Password spying and snitches – network monitor Wireshark
The Github project WPScan allows you to scan WordPress for vulnerabilities!
The No.1 network sniffer is Wireshark. The shark can record and analyse internet packets passing over the network.
Analyse WordPress – Wpscan

Where are the gateways? The ports – Postscanner
Every server has vulnerabilities! You just have to find the vulnerabilities! To find the right entrance, you use port scanners. One of the 63000+ doors the server must use to interact with the outside world.
Scan the whole internet – Masscan
Masscan claims they can scan the internet in 5 minutes at 10 million packets per second. For deep analysis, nmap is better thought of.
Vulnerability scanner for the whole network – Nessus
How do I find vulnerabilities over the network? Do I have an old, forgotten Windows 95 box somewhere in the company? An outdated backup server? Or an unpatched Smart Home refrigerator that carries out DDoS attacks? Nessus finds all vulnerabilities in the network!
Mobile network and vulnerability scanner – dSpoilt
If you’re looking for a programme for your Android smartphone, you’ve come to the right place with the app dSpoilt. The app can perform network mapping, vulnerability scanning, password cracking and man-in-the-middle attacks.
Enterprise risk scanner – zBang Tool
With zBang, you can determine the risk in your organisation by having the software detect possible admin accounts and scan the network. If you use the tool, your company’s infrastructure should be more visible.
What’s on the network? Network Scanner – Angry IP Scanner
AngryIP Scanner can scan the Internet or local networks. Set an IP range, export the results and evaluate your network.
Other tools
Erase data forever and ever – DBAN
When you delete files in the recycle bin, they are not deleted but only marked as deleted. The software DBAN guarantees a secure deletion solution by overwriting zeros, the deleted file.
View and modify protected code – Resource Hacker
Resource Hacker software can decompress .exe and .dll files so you can change the code. Criminal hackers deliver their programme as a Trojan or virus. Use Ressource Hacker to change the GUI, functionality, security restrictions, update mechanisms, etc. of the target programme.
Forgotten password in code? Password tracker – truffleHog
Have you ever forgotten a password in code? Many Github repos contain passwords that the developers “actually” never wanted uploaded. The nimble software TruffleHog finds all strings with high entropy (mostly passwords) in a repo.
Link Analysis Tool for Social Engineering – Maltego

Social engineers use Maltego as a graphical analysis tool to link information. This tool is used by forensic investigators looking for criminals, savvy journalists and researchers
Stay undetected and cover up mistakes – VPN
Do you feel like you are being watched by governments, the NSA, criminals, colleagues and others when you surf the net? Are you surfing websites that you don’t want other people to know about? Then you need a secure tunnel into the net. Black hats use a virtual private network to remain unknown in the event of unsuccessful hacks.
Which hacking tool is missing? Write it in the comments!