How can I send a file securely?
I’ll explain four methods, varying in security and complexity.
Let’s start!
Sending files securely – only for professionals?
You need to get confidential documents from A to B quickly. The postal service is unreliable and not a secure partner. Some critical documents should not be seen by secret services, states or criminals. But how should you send files securely?
“Encryption” is the magic word here. Most people use solutions that appear to be secure, but have only a very low level of security. You don’t have to become a computer science professor (aka cryptologist) to send files securely. However, you should always avoid the following insecure methods:
Popular and insecure methods
The TLS / SSL email with attachment
Many email providers advertise secure email. Cryptic abbreviations like SSL should create trust. But, often only the transfer from your computer to the provider is “secure”.
The mail with the attachment can be seen by the provider, the state and the (local) Secret Service. The transfer between the providers can be insecure because they do not have to adhere to the standards. This can take place uncontrolled and unencrypted.
The recipient himself can be insecurely connected to his email provider, so that criminals intercept the mail on the route between provider and recipient.
Known messengers with file send function
Some messengers offer a file / data send function. This makes it very convenient to send files to a telephone number. Often the size is limited.
Are these variants secure? No.
Large tech companies now scan content for “forbidden” images, so the data must be unencrypted.
Transferring via the cloud
Encryption takes place during transfer with HTTPs. In principle, this is a secure method.
Because at least 95 % of the cloud servers are not encrypted, this method is just as useless.
Most providers protect your data “at rest” only through several physical barriers in a data centre (walls, locks, barbed wire). Anyone who has access to the server can see the file.
Popular file sharing platforms like BitTorrent make sharing (illegal) content easier. P2P sharing is a good approach but not a solution for secure transfer of secret data.
4 secure methods
I present you 4 levels of security. The higher the level, the more complex it is to implement. Even level 1 is strong enough to withstand a normal attack by a Secret Service and quantum computers.
Security level 1 – Minimal security
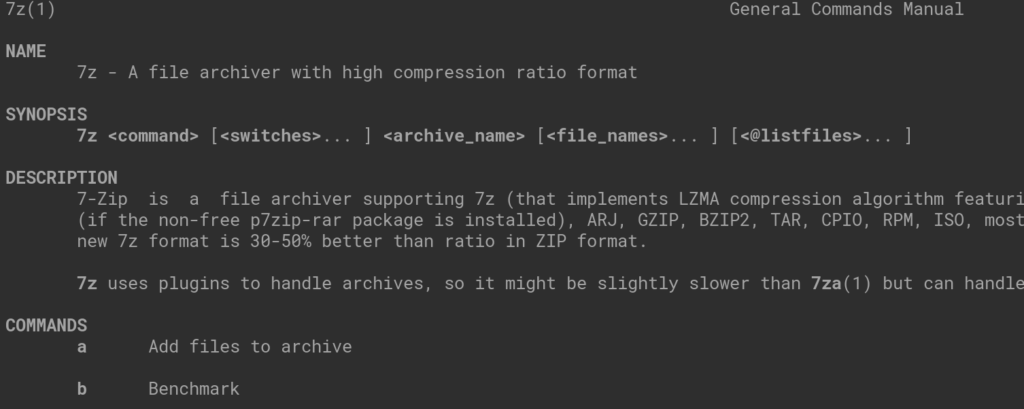
You should start by encrypting the files on your laptop locally, which is not infected by malware.
The programme 7z encrypts an archive with AES-256, which independent researchers have considered secure for 30 years. In relevant internet forums, participants claim that this encryption is not secure enough against quantum computers. This is not true.
Use a random 10-character password that is a crazy mix of all the symbols, letters and numbers on your keyboard. You transmit this password in a secure email or give the password to the person during at a physical meeting.
You can now upload the encrypted archive to a trusted cloud platform.
Security level 2 – Contractual trust
Encrypt the file as in level 1, using a 14-digit password that contains random numbers and symbols (high entropy).
Instead of uploading the file to any cloud, pay attention to its standards. ISO27001 certification, external pentesting and compliance with DSVGO is a minimum standard. Regulated companies that have a certification work differently than companies that quickly set up a few servers. Structure, audits and rules are the key here.
You can’t buy this effort for €4.99 in the supermarket, you have to pay money for this service.
Security level 3 – Full control
Encrypt the file as in level 2.
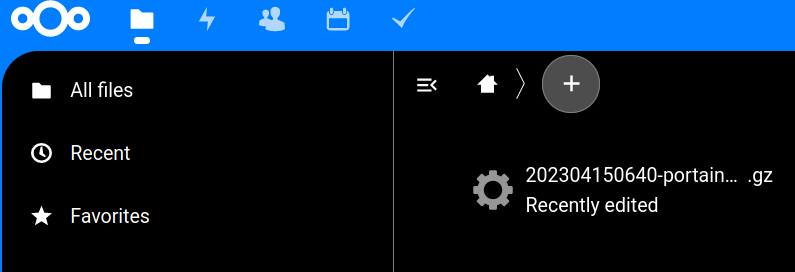
Instead of uploading the file to a cloud, you should upload it to your own cloud instance. This can be your office machine or your home server (see instructions).
In principle, you can only trust yourself and recognized encryption algorithms. The effort to set up a home server decreases from year to year.
The containerization system Docker, virtual systems and scripts allow a very simple operation. For most internet connections, you need a public IP because most internet service providers want to make more money.
Your partner can then log into your cloud and download the content via HTTPs or SFTP.
Security level 4 – Paranoia
You only need to perform this level if you are Snowden 2.0, a persecuted journalist or a Secret Service agent with a nuclear warhead code.
This method has been proven to provide the best mathematical method of encrypting content:
With the One Time Pad, you have to create a long string of digits with real random 0s and 1s. The important thing here is the randomness. If this numerical text can be reconstructed with a formula or if it repeats itself every X characters, then the encryption is quickly cracked.
If you want to exchange a 1 GB file, you need a One Time Pad with 1 GB or more. You can only use this once. When you meet your buddy for the first time, you need to have a One Time Pad on hand to transfer the content securely.
Send anonymously
For some journalists and persecutees, it may be important to transfer files anonymously.
The methods presented prevent a third party from reading. The third party will see a jumble of letters, but will be able to track that a file / files have been exchanged between the journalist and the recipient.
You can only hide the IP with an overlay network. You send the file via several “unnecessary nodes” to hide your original IP. An overlay network is e.g. Tor. I have already created a tutorial here.
Keep in mind that with large files the transfer can take a long time. The transfer via the nodes is costly. Volunteers donate server power, which does not have infinite bandwidth. Try splitting the download into several files and logging them in at different times. Depending on the time of day, the upload may be faster.
What do quantum computers crack?
Quantum computers are still not ready for production in 2024.
It may be several years before they are in data centres around the world. They are not better than normal computers, but can calculate some problems very well quickly – others no faster than a normal computer.
The big danger today is that you send a document, which the third party stores and then decrypts in 10 – 40 years with a quantum computer. Some documents will still be valid in 10 – 40 years.