How secure is an encrypted phone? How does it work?
This guide explains the phone + how to make your own for free.
Let’s get started!
What is an encrypted smartphone?
A encrypted phone is a smartphone or keypad phone built for encrypted and non-interceptable communication. The recipient needs a compatible encryoted phone for the software to establish secure end-to-end encryption. Communication can take place via short messages, video conferences or telephone calls.
For bug-proof communication, you need not only a secure phone, but also a suitable environment – a sound-proof booth without bugs.
How bug-proof are crypto mobile phones?
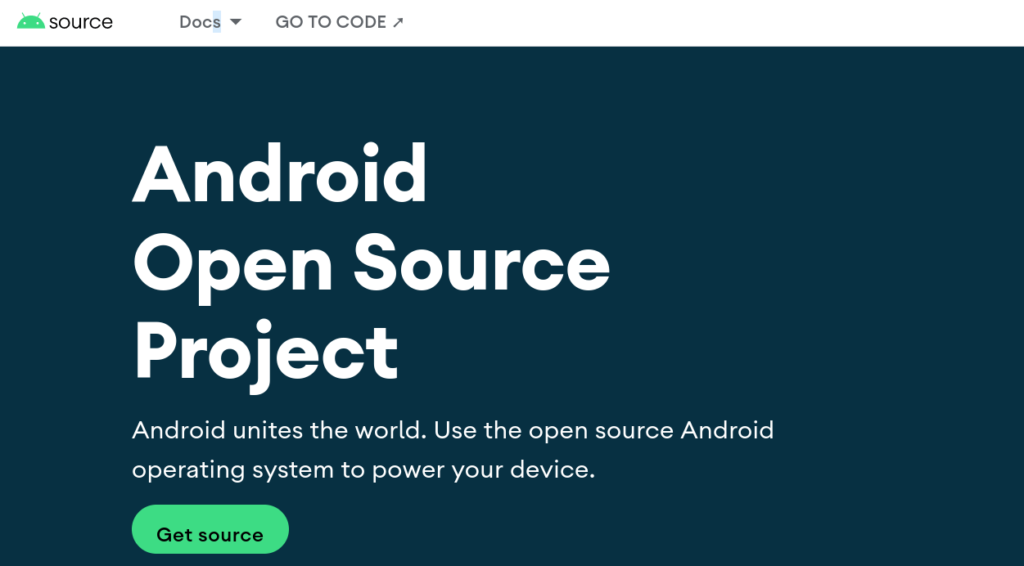
A crypto mobile phone is usually a customised Android smartphone with a regular SIM card. Android is an open source project by Google and the source code is freely available. Because the source code is freely available, 1000s of developers can verify that the code is secure.
Crypto phone manufacturers are “trying” to make the device even more secure. The manufacturers install messenger and email apps that their customers can use to communicate with each other. The manufacturers usually chooseapps thatsend messages encrypted end-to-end .
Do I need a encrypted mobile phone?
High-stake people with an increased risk of eavesdropping buy such devices. These include politicians, bankers, CEOs, actors and other well-known personalities. On the other hand, criminals buy these devices to communicate between each other.
Ways in which the state can eavesdrop

In case of reasonable suspicion, the judiciary has the possibility to question the internet service provider such as AT&T, Telekom or Vodafone. They have to store all conversations and messages of the last 14 days.
Correctly encrypted messages remain unreadable even for the internet service provider.
Steffen Lippke
Trust or mistrust …
The big problem with many secure phone vendors is that they do not publish their code. The security of the mobile phone depends 100 % on the competence of the vendor. If they screw up, anyone can listen to your calls.
Sometimes, the police have some capable consultants who find a way into the “uncrackable” mobile phone. They use so-called 0-day exploits for the break-in. A 0-day exploit is a vulnerability that is not yet known to the vendor. The vendor of crypto mobile phones promise a lot, although they are just a “normal” company.
I show you a better method in the section “How can I make my smartphone secure?”
Steffen Lippke
Fake secure mobile phone marketing
Many customers believe that their crypto mobile phone is secure if the user interface uses a dark mode with white console writing.
Dialogues are peppered with encryption symbols and “cryptic abbreviations”. Is this trustworthy?
What is the most secure encryption?
AES encryption has been considered unwaveringly secure for 30 years. The standards body NIST selected it as the “gold standard” for everyday use. Messengers / websites like Signal and many others use this transport encryption. However, the data is often unencrypted on the provider’s server. You need end-to-end encryption!
In addition, there is another simple method that is mathematically proven to be unbreakable:
The One-Time-Pad!
A one-time pad is a file with many truly randomly generated 0s and 1s – the key. If you apply an XOR operation between the message and the one-time pad, you encrypt the text. If you perform the same operation with the same one-time pad on the recipient, then the recipient receives the plaintext through the property of the XOR operation.
Because the one-time pad is completely random, no quantum computer or normal computer can compute the clear message in a million years. The one-time pad is equal to or longer than the file to be encrypted.
The disadvantage is that both parties must have the same one-time pad and they must renew the pad when the key is used up.
How can I make my smartphone secure?
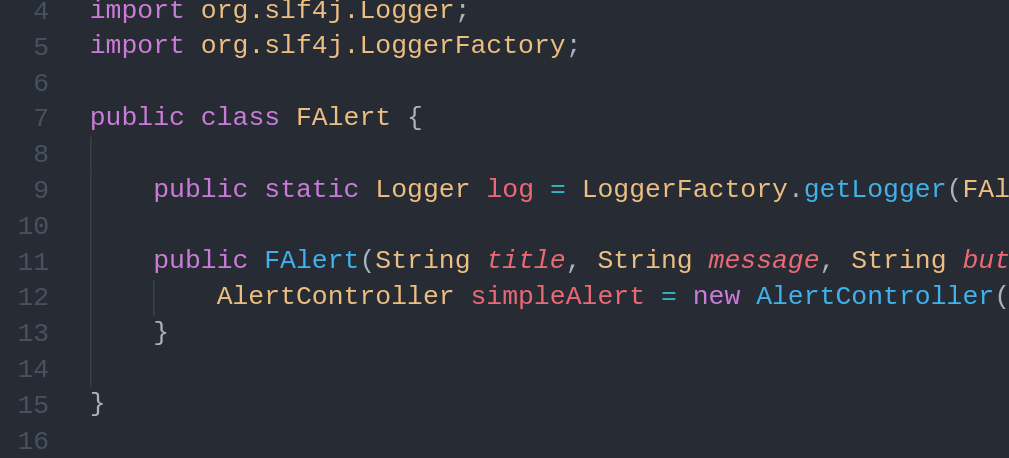
Before we start, we need the following basics: secure phone vendor and the Apple company use source code concealment for “better” security. These manufacturers only deliver the binary code, which the manufacturer complies from the source code. Binary code is very difficult to read and bugs and vulnerabilities are difficult to find.
Anyone can read open source code. The more popular the code is, the more secure the code is, because many pairs of eyes check the code for security. That is why well-known open source software offers the highest security.
Are encrypted phones legal?
Yes. In Germany and the most western countries, you are allowed to send encrypted messages and make encrypted calls.
A vendor in Germany is not allowed to send SIM cards with the device. Every SIM card must be personalized in Germany (personal verification required). Before 2017, any fool could buy a SIM card and pretend to be someone else to the internet service provider.
Create your own encrypted mobile phone
1. Choose
Use or buy an Android smartphone. Apple devices are not suitable because they do not run Open Source OS. “Popular” devices are particularly suitable. You will find exact instructions per device and official ROMs because a voluntary community maintains them.
2. Backup
Back up all your data. Click here for the guide. The following steps will reset your smartphone ! Follow the device-specific instructions exactly, so you don’t create a brick / electronic waste.
3. Unlock
Unlock the bootloader to root the device. This step will result in you no longer receiving support from the manufacturer unless you completely reverse the steps.
4. Install
Install an alternative ROM such as Lineage on the device. The Lineage ROM uses the secure LinuxSE (for Security Enhanced) operating system as its base.
5. Choose communication
Do not install your normal apps on the device. The fewer apps you have installed, the less vulnerable you are. You can use the chat app Signal for end-to-end encrypted communication. Encrypted phone vendors does not do things differently. They just suggest that they are “experts” and know their stuff.
Some portray their own platform as “unhackable”. In reality, users are at great risk if the police or other criminals find another way into the system.
Steffen Lippke
How can I still communicate securely?
If you have a (foreign) laptop or other desktop computer at your disposal, you can use the operating system “Tails”.
Tails is a Linux operating system that is stored on a USB stick. As soon as you shut down the computer, all changes and traces that you made during the session with Tails disappear. The operating system is a live operating system that only keeps the data in the main memory. If the power fails, the changes are gone.
The next time you start Tails, the USB stick is back to its original state. In Tails you can dial into the TOR network via the secure browser Firefox. The free TOR network makes tracking of users almost impossible and you can use parts of the internet and darknet.
On the darknet, you can find legitimate services that you can book or use for free to communicate with other people. These include chat programmes, end-to-end encrypted emails with PGP or file sharing platforms for documents.