Hacking an Instagram account – is that possible?
I’ll show you which 11 ways are feasible without hacking knowledge and how to protect yourself from hackers!
Let’s begin!
- 1 How to do it without computer knowledge?
- 2 11 Social Engineering Technical Hacks
- 2.1 #1 False facts (pretexting)
- 2.2 #2 Instagram Sweepstakes (Reciprocity)
- 2.3 #3 Forgotten USB stick (USB dropping)
- 2.4 #4 The most useless support (authority)
- 2.5 #5 The Fingerprint Trick (Replay Spoofing Attack)
- 2.6 #6 Software vulnerabilities – using exploits
- 2.7 #7 The geeks’ super crowbar (Bruteforce)
- 2.8 #8 Insecure smartphones after 6 – 24 months
- 2.9 #9 Post-its hack – not too much effort
- 2.10 #10 Errors are programmed in
- 2.11 #11: Find data leaks use
- 3 FAQ
How to do it without computer knowledge?
Social engineering is a strategy that tries to manipulate people rather than computers. By the end of this guide, you’ll have full access to an Instagram account without spending money on useless spy apps or fake hackers.
This strategy can be executed by anyone without IT knowledge. Social engineering is what spies use to achieve their goals. The success is based on people’s natural thought patterns (Congnitve Bais). The attacker tries to manipulate the victim with words, images, sound and / or text.
If you want to work technically on the computer, then jump to tip 6 to 10 to be able to hack into an account. For technical hacking, you need a little more computer basics. Read the full guide.
The following 5 factors are the basis of social engineering:
Social confirmation
The hacker asks the victim to open a security door, for example.
The hacker claims that the victim’s boss behaved in the same way (lie). The hacker twists reality to manipulate the victim. The criminal tries to manipulate the victim with a social proof.
Self-commitment Consistency
A person wants to appear consistent to the outside world with their behaviour, words and decisions. Behaviour that is not consistent makes a person untrustworthy. Hackers manipulate people with statements such as
“You’ve always done it this way – why not now?”
Social hackers
OR
“Didn’t you have this goal written all over you?”
The criminals can change a rock-solid mind or will of the victims by working out step by step no concessions.
As I do, you will do – Reciprocity
I do you a (small) favour, and therefore you will do me a big favour.
The hacker tries to gain your goodwill with a small favour, e.g. forwarding information or holding the door open. You thank him and say
“… Thank you – if you need anything, get in touch with me”.
The victim
A day later, the hacker asks the victim for a unreasonable favour. The other person wants to “return” the favour and usually agrees!
“Can you let me through this door (into the top secret area)? My interview for my promotion starts in 3 minutes in room XZ.”
The Social Hacker
Establish real fake friendship
White-collar spies try to build a friendship over weeks or years with small favours (see Rule 2). At a later stage, the hacker manipulates the victim. The hacker asks the victim for a favour that the victim may never agree to (e.g. enter a password for a high-security computer).
The great fear of loss
The hacker gives exclusive profits, rewards and gifts. The victim is supposed to bite at the bait, so the victim gives away sensitive information.
“You can become our company’s employee of the year if you describe the patent for the prize endowment to us in more detail.”
The Social Hacker
Am I the right type for social engineering? Here are a few pros and cons for this form of hacking:
You can ..
- … penetrate systems without having the technical knowledge about the systems.
- … penetrate systems in the most inconspicuous way (via a legitimate employee account).
- … penetrate systems that cryptologists and IT security experts consider to be secure according to the current state of the art
Remember, you need …
- … a secure, flawless appearance in spoken or written form in the language of the victim.
- … extensive research on the victim.
- … a victim who is not briefed with social engineering attacks.
- … a plan B if the social engineering attack is noticed.
- … knowledge about the manipulation techniques and their correct application.
Application in “real” life – Social Engineering
In real life, corporate spies aka James Bond and shrewd governments use social engineering to steal ..
- Patents in development / leaks (products)
- Money / money laundering / tax evasion
- Price lists / design of product X / specifications
- Recipes / formulas / chemical substances
11 Social Engineering Technical Hacks
I’ll show you 11 hacks to invade your victim’s (partner, friend, relative) Instagram. One or more strategies can lead to success depending on the situation. You may need to combine or recreate the scenarios appropriately.
#1 False facts (pretexting)
Pretext false facts: Call your victim with an unknown phone number. Explain that you are an Instagram employee who wants to push the newcomer influencers.
“To set up the permanent Instagram reach boost, I need their username and password, so we know we’re promoting the right one.”
Social Hacker on the Phone
#2 Instagram Sweepstakes (Reciprocity)
Raffle among the best Instagram accounts: call your victim with a suppressed phone number.
Pose as a TV employee looking for “hidden” Instagram stars for a casting call. Say that your victim is among the top 5 content creators who have a chance to win a casting with money.
#3 Forgotten USB stick (USB dropping)
Prepare a USB stick with malware:
- Download a keylogger
- Drag the keylogger onto a USB stick
- Place it on the victim’s desk
- Wait until your victim uses the USB stick and runs the TopSecretInformation.exe (keylogger)
- After the victim uses Instagram, you can analyse the saved entries and log in yourself.
“Help” via email:
- Create a fake email account, e.g. instasupport@gmx.de or InstagramFacebook@t-online.de. Professionals secure domains such as instagram-vip-support.com and send so-called cookies or JWT tokens from there so that you are not asked for your password every time you open the app.
- Name yourself “Instagram Support”.
- Write an email with the following content:
Due to a hack, passwords need to be reset.
Insta Support Fake
Please, send the following form back to this mail. Please, include your old and new password.
#5 The Fingerprint Trick (Replay Spoofing Attack)
Fingerprint Replay: Many Instagram users log into their smartphone and Instagram with their fingerprint. In the past, Samsung and Apple sensors have been successfully tricked. This guide explains why.
The victim distributes their “password” as a fingerprint almost everywhere the victim touches something. Pick a print that is easily recognisable and make a copy.
#6 Software vulnerabilities – using exploits
So-called cookies or JWT tokens make it possible not to be asked for the password every time the app is opened.
Instagram vulnerabilities: Do you think that the operator Facebook has built its platform Instagram 100% secure?
Nope. On 22 February 2020, hackers were able to break into Instagram profiles via the password reset feature.
Has your victim not updated the app yet?
An update guru
From time to time, hackers find vulnerabilities in apps so ANYONE with the right exploit program can get into the app. Even in the past, hackers were able to access users’ personal information
Meta can never plug all vulnerabilities.
#7 The geeks’ super crowbar (Bruteforce)
Try Bruteforce: Do you know that your victim doesn’t use the best passwords in the world? Then try the following passwords.
- 123456
- 12345678
- the name of your pet or partner
- date of birth
- Favourite food
#8 Insecure smartphones after 6 – 24 months
Once you have control of a phone, then you have control of all apps (with Instagram). If you want to get into your victim’s phone, try my phone hacking tutorial.
The app (Instagram) is only as secure as the device being used. If the device doesn’t have a PIN, then you have instant access to the account.
#9 Post-its hack – not too much effort
The Post-it trick: Has your victim written down the passwords somewhere? Maybe as a Post-it on the screen, on the back of the mobile phone or in a personal notebook? Password cracking can be so easy.
#10 Errors are programmed in
Instagram’s developers (Meta) spend a lot of time making their app secure. They secure the app with encrypted internet traffic and use multifactor authentication (fingerprint).
Developers are human and humans make mistakes. Therefore, there are also bugs (called vulnerabilities) on Instagram. You need to find these bugs to demonstrate a successful hack.

I have written a complete guide to learning to hack. Honest people report the vulnerabilities to the Facebook corporation and receive compensation of up to 1,000,000 euros for their efforts. This sounds totally exaggerated, but Meta pays this much for critical vulnerabilities because they could mean their financial demise.
#11: Find data leaks use
A hacktivist is a person who hacks an application to protest against the company behind the application. The hacktivist commits a crime but does not benefit from the hack (e.g. a form of self-enrichment).
Meta (formerly Facebook) is a company that many hacktivists have caught in the crossfire. The hacktivists post the captured data on the Darknet, which you can only access via a special browser. Read more in the Darknet guide.
The captured data is freely accessible to the public in the Darknet and the government or a company itself cannot do anything against data once it has been published there.
FAQ
How can I find out my Instagram password?
You want to hack your account if you have forgotten your password? In many cases this is not necessary. I have put together Forgotten your password! What to do? tutorial. Resetting your password can be done in several ways.
How can I find an Instagram hacker?
As already explained in the Darknet tutorial, you have no guarantee that the hacker will do anything for you after your payment in cryptocurrencies. You can find apps or offers from hackers on the internet that offer this, but you have no way of getting your money once you have paid the hacker.
Hacking Instagram followers – is that possible?
Wouldn’t it be nice to have 10,000 more followers? You want to earn money with product placements and post all day?
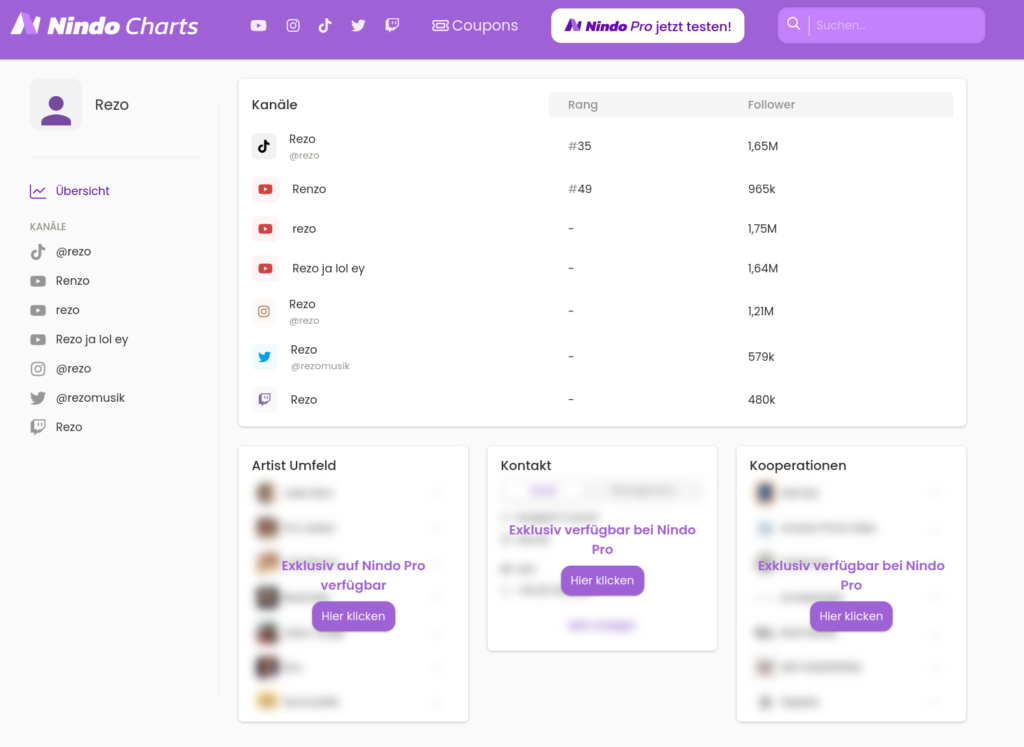
No!
There are dubious providers on the internet who will get you “10,000 followers” for money or for free. In reality, they want to know your password to enrich themselves.
Steffen Lippke
How can I prevent being hacked?
Use the following 6 strategies to secure your Instagram account
- Log out after every use (don’t use cookies). Many hacked popular YouTubers say they use MFA / 2FA, but hackers still get into the account with a malware and cookie.
- Avoid using third-party apps. These access your Insta profile and can be another gateway for hackers.
- Choose strong passwords (12 characters, not pawned) – don’t change them every 90 days – no, you must keep your strong password secret and only change it if you suspect a hack
- Back up all your original pictures, texts and videos from your camera folder. If Instagram has a bug or you get hacked, you can upload them all again.
- Use Instagram’s two-factor authentication
- Remind yourself of the most important social engineering attacks at regular intervals.