Is hacking illegal?
Are all hackers criminals?
I would like to clarify this question in this article and give a comprehensive overview of the use of hacking tools.
Let’s begin
Representation in Film, Television Press
News channels often show similar clips when the newscasters report a hacking attack at company Y or government agency X.
A hacker sits in front of his laptop in the dark wearing a hoodie.
Green letters appear on the screen on a black background and numbers fly across the screen. The face is hidden by a pale mask with a moustache (Anonymous mask).
The media associate hackers with malware, fake passports, drugs and arms trafficking. Is this correct?
Steffen Lippke
What is hacking?
To find out whether hackers are criminals, we should take a look at the definition . What is hacking and how can we correctly classify the term?
A hacker is a person who tries to achieve a goal or overcome a challenge using their technical knowledge and a computer. The hackers’ path usually does not take a standard route.
(Adapted from Wikipedia English)
Examples of hackers
Read through the following examples and consider whether the “hackers” are dangerous or not:
- Max works in a software start-up. He is programming a completely new product using an unconventionally ingenious method.
- Jan tries to make his computer faster. He makes changes to the operating system (Linux) so that the software uses his hardware even more efficiently.
- Phil tries to adapt a chat programme to his own needs in a way that no one else would (novel shortcuts, different icons).
We can include the three people presented under the definition of hacker. Max, Jan and Phil are not committing a crime from a common sense point of view.
(Opinion – Steffen Lippke)
Evil hacking = breaking a lock?
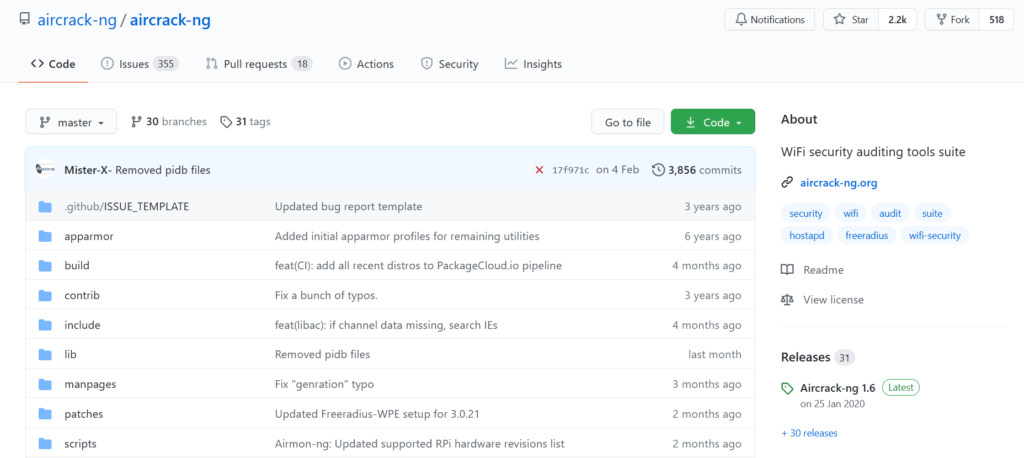
Hackers can use so-called hacking tools (software for hacking). Read through the following three examples and decide whether the behaviour is criminal.
- Anna has lost her Bitcoin key and is trying to gain access to her own wallet by automatically testing passwords (brute forcing software from the Darknet).
- Florian has forgotten his Windows password and resets his Windows password with special software from the internet so that he can log in again with a new password.
- Johanna has a profile on a social media platform. A hacker changes the password of her account so that Johanna can no longer log in. Johanna tries to use the hacker tools to gain access to her own account.
Is this illegal? Can the use of software be a criminal offence?
Ethical Hacking – The Good Side
When computer geeks search for vulnerabilities for companies, computer scientists call this activity ethical hacking. Before a criminal finds a vulnerability, honest computer scientists are supposed to warn the company of a weakness so that they can quickly improve it.
Reaction from companies
Not every company understands the meaning behind ethical hacking. That is why companies react very differently to Ethical Hackers:
- The company rewards the Ethical Hacker with 1 million dollars or offers the pentesting job.
- Other companies actively search for Ethical Hackers via a bug bounty programme. For them, it is quite normal for an Ethical Hacker to contact them. This puts the company in contact with capable geeks.
- The company politely thanks them.
- The company sues the Ethical Hacker. This lawsuit should usually be dismissed by the court because the Ethical Hacker is not a criminal. These companies can do nothing with ethical hacking. These companies should urgently look into IT security.
Large companies such as banks do hacking professionally. The EU / law imposes many guidelines on the financial sector regarding IT security. Ethical hackers in large companies are divided into two groups:
RED: These geeks try to attack company systems “like a real criminal”. They are supposed to penetrate the system unnoticed and document all vulnerabilities and data leaks.
BLUE: The geeks are supposed to prevent the RED team from succeeding (and detect hacking attempts). If the RED team succeeds, the BLUE team has to upgrade their systems with the collected knowledge of the RED team.
A dance on the razor’s edge
For example, the hacker must be able to prove a data leak (public viewing) of customer data without looking into the data, because otherwise he would be breaking the law. He may only view the directory, but not click on the customer data.xlxs.
Some companies are careless with their data. They unintentionally publish data on the Internet that hackers can find. Translated into reality, this means that the ethical hacker finds a file folder on the street, but is not allowed to open it and leaf through it.
Dual Use Tools – A Hacker’s Screwdriver
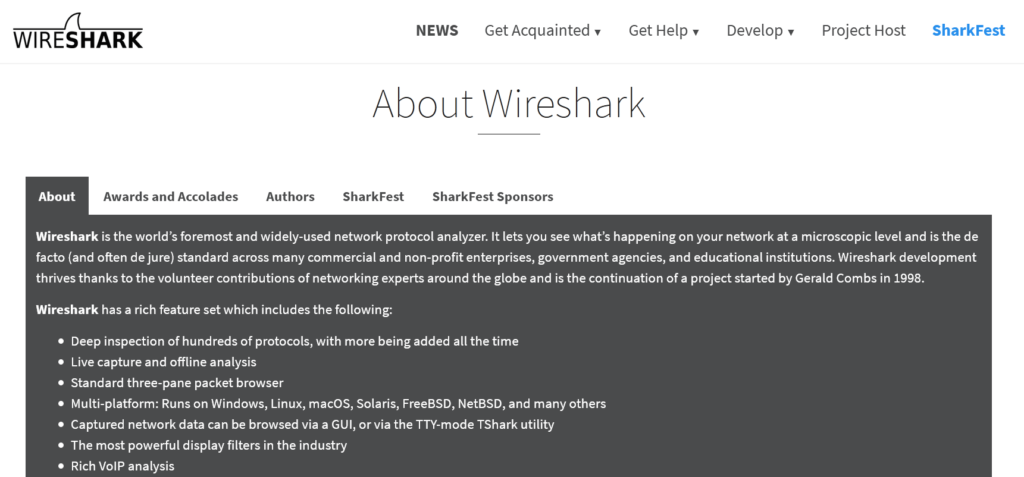
Wireshark is a fine example of a dual use tool. The software is an essential piece of equipment for a network administrator to configure the network. The system admins can identify problem in the network with Wireshark and can specifically remediate them.
On the other hand, hackers can use Wireshark to read passwords sent by a computer via HTTP without S (for secure, port 80) (yes, such sites still exist!).
Another tool is RainBowCrack, which helps to crack passwords with brute force. Hackers can use the tool to gain access to various online accounts. The prerequisite is that the hashed password database is publicly available.
Hacking tools or dual-use tools
A knife is comparable to a hacking tool (dual-use tool):
- The knife is used by a cook to prepare a good meal (causes a benefit)
- The same knife is used by a murderer to stab a victim (causes a crime)
Can the law ban a knife? The same applies to hacking software (dual-use tool):
- Hacking tools help developers build reliable software. System admins can use such software to carefully configure systems.
- On the other hand, criminals can use these tools to detect and attack vulnerabilities.
When the police search the Internet for such prohibited tools, identifying software as a pure tool is difficult for criminals.
Use of dual-use tools
Surely these tools should be banned?
No. Ethical hackers need this software to restore access to lost admin accounts.
The company is desperate because they can no longer get to the records in the database. The system admin died in the road accident and nowhere to find the password. Now an ethical hacker comes into play. He uses RainBowCrack for a possible legal use case.
Steffen’s example